Specious one bedroom available
April 18, 2013 § 2 Comments

‘Oh!’ cried Mrs. Skewton, with a faded little scream of rapture, ‘the Castle is charming!—associations of the Middle Ages—and all that—which is so truly exquisite… Such charming times!… So full of faith! So vigorous and forcible! So picturesque! So perfectly removed from commonplace! Oh dear! If they would only leave us a little more of the poetry of existence in these terrible days!’… ‘Those darling byegone times… with their delicious fortresses, and their dear old dungeons, and their delightful places of torture, and their romantic vengeances, and their picturesque assaults and sieges, and everything that makes life truly charming! How dreadfully we have degenerated!’
While Dicken’s Dombey and Son is not one of the books included in Castles: an Anthology, Mrs’ Skewton’s medievalist rhapsody may well have been the guiding principle behind the selection of the 160 items included in this online collection from the British Library, which includes archaeological treatises, antiquarian histories, images, Gothic romances and pseudo-histories featuring picturesque dungeons, sieges, knights and fair maidens. With three exceptions from the 18th-century and one from the 17th-century (Dryden’s King Arthur, 1691), all of the items in the Castles Anthology are digitized 19th-century primary sources. The reader is therefore introduced not only to histories, images and fiction associated with medieval castles, but experiences these sources through the lens of Victorian culture and taste. Hence the result is a fascinating glimpse of Victorian medievalisms, viewed through a 21st century interface. read more
PHOTOGRAPH: Angela Strassheim
He wasn’t listening. That was the worst of people like that; they were a monologue – killers are like the army, dull and dangerous simultaneously
December 24, 2012 § Leave a comment
Late one Friday evening, my phone played the codec-out sound from Metal Gear Solid, and an email arrived. My stolen laptop had been taken online, and now — like a resourceful kidnap victim — it was phoning home, unknown to its captor. The laptop was beaming back all the information needed to rescue it. And so began one of the strangest episodes so far of my life with technology.
The laptop had been stolen the previous day. I was working in one of the non-public Reading Rooms of the British Library in London. As usual, I left the laptop at my desk when I went to lunch. But this time, when I got back to my desk, it was empty. Damn and blast. CCTV didn’t identify the malefactor, so I went home and changed all my internet-service passwords. I hadn’t lost any work (thanks to Dropbox), but the machine wasn’t insured, and it still felt like a violation — not just of my own distributed, semi-cyborg self, but of the Library as well.
And this wasn’t just any laptop; it was my laptop. It’s not uncommon for us to see personalities in objects, and many people develop a sentimental attachment to their tools. A cook might speak fondly of a particular battered pot, and reminisce about the pungent stews of goats’ feet or bleeding-edge foams made in it; well, this was the Macbook Air on which I’d angrily hammered out my new book, as well as writing tens of thousands of words of other literary and cultural spleen. We’d been through a lot together. Luckily, nine months ago, I had installed some eldritch security software, the open-source Prey. And that’s how, the evening after its abduction, my laptop began calling for help.
I clicked on the link. The Macbook had taken a photograph with its webcam, unknown to the person using it. I saw a young man in an ordinary-looking apartment, shot from a low angle (he was probably using it on his lap) and smiling to someone offscreen. My laptop also told me that he had bypassed my login and created a new user account. A screenshot showed that he was running Apple Software Update. (You don’t want out-of-date system software running on your stolen laptop. That would just be embarrassing.) Triangulating local wifi signals, the laptop reported a rough location on a Google map: a street in Stratford, east London. It told me its router’s IP address, and the name of the wifi network it was connected to. “Friendz.” That just added insult to injury. These clowns nick my laptop, and call their home network “Friendz”? With a Z? Seriously? I might have had some respect for them as criminals if they had called it “Raffles”. Or even “Hamburglar”.
To receive this report was both amazing and deeply odd. Thanks to Prey’s stealth technology, I was now engaged in an amateur police surveillance action, a voyeuristic keyhole-peeping. I forwarded the information to the law-enforcement professionals, the Metropolitan Police, but I couldn’t shake another weird feeling. I knew it was just a machine running instructions, but it felt as though my computer was sentient, and pleading in a faint but very precise voice to be liberated. It was, I decided, uncanny. More than that, it was a uniquely modern species of the uncanny that in Freud’s day simply wasn’t possible: spying in near-real-time on a thief, by means of the stolen object itself, which had, or so it seemed, come to life. Call it the cyber-uncanny. read more
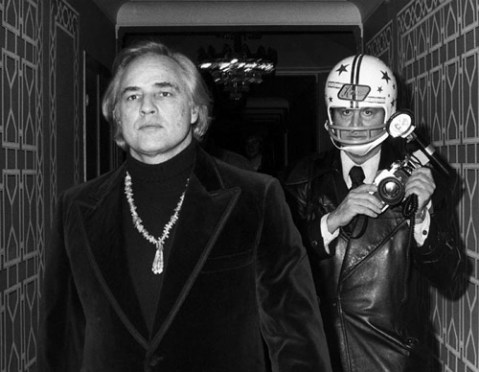
PHOTOGRAPH: Ron Galella