Repeat after me: banks cannot and do not “lend out” reserves
August 15, 2013 § Leave a comment

Back in December 2012, we were bombarded with a campaign to save the free Internet. We were told that the ITU, the UN’s telecommunications body, was planning to take control over the Web during an intergovernmental meeting. A large coalition of private enterprises, activists and some governments (including the US government) came out in strong opposition to this move.
The story went something like this: the Internet is free and nobody owns it. Repressive regimes (Russia, China and Saudi Arabia were often mentioned) want to take control to make it easier for governments to keep an eye on their citizens. Any change to the current open state of affairs is bad.
The ITU-12 conference came and went, and it became evident that as far as evil takeovers went, this one had been a rather poorly organised one. Nothing changed. The Internet had been saved. As you were.
One of the things that always struck me about this campaign was the assumption that the Internet is free. While it is true that in theory anyone can create their own network and join the Internet, the idea that this makes the Web a free and open space seems to be an illusion.The problem is that we tend to think of Internet governance in the wrong terms. We concentrate on the existing multi-stakeholder institutions that have decision-making power over domain names and protocols as the governing bodies that exercise some level of control over the Internet. But we seldom think of the reality. The Web is more centralised than we would like to believe, few countries and a handful of private companies have a disproportionate amount of power with regards to the existing architecture. This is where the real power lies.
The distributed and open Internet is a worthy cause to support. Information wants to be free, but somebody has to pay for it. So besides the common fear of governments prevalent in online communities, we need to take a hard look at the way in which the Internet has become a sizeable business, and how some few companies command a disproportionate amount of power. These companies no longer respond to self-imposed promises not to be evil, their reason for existing is to make a profit. The NSA revelations have uncovered a public-private conglomerate of gigantic proportions, with the US government and many US-based companies at the centre. Each new revelation has uncovered layers of collaboration that many suspected, but the reality seems to surpass even the worst conspiracy theories.
The PRISM program unveiled collaboration at the service level. Most of the largest Internet services are based in the United States, so PRISM uses that fact by co-opting these companies into allowing surveillance of its users. One PRISM slide boasts that most communications pass through the US, while another chronicles the dates in which companies like Microsoft, Google, Yahoo, Facebook and Skype were added to the program.
However, to me the most surprising (and chilling) revelation of all is XKeyscore, which implies a level of collaboration at the basic infrastructure level that few suspected. XKeyscore is a NSA program that allows intelligence agents to retrieve metadata and content about anything a user does online simply by providing an email address. Unlike PRISM, which relies on the service providers, there are strong implications in the XKeyscore presentation that lead me to believe that the US intelligence services are able to snoop on Internet traffic almost at the basic level. First there is the fact that XKeyscore is not centralised, it consists of a number of 500 Linux servers located around the world.
Then there is the fact that XKeyscore can be used to obtain an amount of data that cannot come from service collaborations. read more
PHOTOGRAPH: Lee Jackson
I have found out what economics is; it is the science of confusing stocks with flows
August 5, 2013 § Leave a comment
Brendan O’Connor is a security researcher. How easy would it be, he recently wondered, to monitor the movement of everyone on the street – not by a government intelligence agency, but by a private citizen with a few hundred dollars to spare?
Mr. O’Connor, 27, bought some plastic boxes and stuffed them with a $25, credit-card size Raspberry Pi Model A computer and a few over-the-counter sensors, including Wi-Fi adapters. He connected each of those boxes to a command and control system, and he built a data visualization system to monitor what the sensors picked up: all the wireless traffic emitted by every nearby wireless device, including smartphones.
Each box cost $57. He produced 10 of them, and then he turned them on – to spy on himself. He could pick up the Web sites he browsed when he connected to a public Wi-Fi – say at a cafe – and he scooped up the unique identifier connected to his phone and iPad. Gobs of information traveled over the Internet in the clear, meaning they were entirely unencrypted and simple to scoop up.
Even when he didn’t connect to a Wi-Fi network, his sensors could track his location through Wi-Fi “pings.” His iPhone pinged the iMessage server to check for new messages. When he logged on to an unsecured Wi-Fi, it revealed what operating system he was using on what kind of device, and whether he was using Dropbox or went on a dating site or browsed for shoes on an e-commerce site. One site might leak his e-mail address, another his photo.
“Actually it’s not hard,” he concluded. “It’s terrifyingly easy.”
Also creepy – which is why he called his contraption “creepyDOL.”
“It could be used for anything depending on how creepy you want to be,” he said. read more
ART: Ernst Wille
Understand death? Sure. That was when the monsters got you
July 1, 2013 § Leave a comment

An extraordinary fuss about eavesdropping started in the spring of 1844, when Giuseppe Mazzini, an Italian exile in London, became convinced that the British government was opening his mail. Mazzini, a revolutionary who’d been thrown in jail in Genoa, imprisoned in Savona, sentenced to death in absentia, and arrested in Paris, was plotting the unification of the kingdoms of Italy and the founding of an Italian republic. He suspected that, in London, he’d been the victim of what he called “post-office espionage”: he believed that the Home Secretary, Sir James Graham, had ordered his mail to be opened, at the request of the Austrian Ambassador, who, like many people, feared what Mazzini hoped—that an insurrection in Italy would spark a series of revolutions across Europe. Mazzini knew how to find out: he put poppy seeds, strands of hair, and grains of sand into envelopes, sealed the envelopes with wax, and sent them, by post, to himself. When the letters arrived—still sealed—they contained no poppy seeds, no hair, and no grains of sand. Mazzini then had his friend Thomas Duncombe, a Member of Parliament, submit a petition to the House of Commons. Duncombe wanted to know if Graham really had ordered the opening of Mazzini’s mail. Was the British government in the business of prying into people’s private correspondence? Graham said the answer to that question was a secret.
Questions raised this month about surveillance conducted by the National Security Agency have been met, so far, with much the same response that Duncombe got from Graham in 1844: the program is classified. (This, a secret secret, is known as a double secret.) Luckily, old secrets aren’t secret; old secrets are history. The Mazzini affair, as the historian David Vincent argued in “The Culture of Secrecy,” led to “the first modern attack on official secrecy.” It stirred a public uproar, and eventually the House of Commons appointed a Committee of Secrecy “to inquire into the State of the Law in respect of the Detaining and Opening of Letters at the General Post-office, and into the Mode under which the Authority given for such Detaining and Opening has been exercised.” In August of 1844, the committee issued a hundred-and-sixteen-page report on the goings on at the post office. Fascinating to historians, it must have bored Parliament silly. It includes a history of the delivery of the mail, back to the sixteenth century. (The committee members had “showed so much antiquarian research,” Lord John Russell remarked, that he was surprised they hadn’t gone all the way back to “the case of Hamlet, Prince of Denmark, who opened the letters which had been committed to his charge, and got Rosencrantz and Guildenstern put to death instead of himself.”)
The report revealed that Mazzini’s mail had indeed been opened and that there existed something called the Secret Department of the Post Office. Warrants had been issued for reading the mail of the king’s subjects for centuries. Before Mazzini and the poppy seeds, the practice was scarcely questioned. It was not, however, widespread. “The general average of Warrants issued during the present century, does not much exceed 8 a-year,” the investigation revealed. “This number would comprehend, on an average, the Letters of about 16 persons annually.” The Committee of Secrecy was relieved to report that rumors that the Secret Department of the Post Office had, at times, sent “entire mail-bags” to the Home Office were false: “None but separate Letters or Packets are ever sent.”
The entire episode was closely watched in the United States, where the New-York Tribune condemned the opening of Mazzini’s mail as “a barbarian breach of honor and decency.” After the Committee of Secrecy issued its report, Mazzini published an essay called “Letter-Opening at the Post-Office.” Two months after the Mazzini affair began, the Secret Department of the Post Office was abolished. What replaced it, in the long run, was even sneakier: better-kept secrets. read more
PHOTOGRAPH: Derek Vincent
Only losers take the bus
April 26, 2013 § Leave a comment

On 11th September 2012, late at night, a group of 4 or 5 people staked out my home. It was only accidentally that I avoided being ambushed (my motorcycle had a flat tire and I thus returned home in a friend’s car). Upon noticing the stalkers I called the police and asked them to come quietly. The police arrived noisily and went to a nearby house first, thus giving the men plenty of time to make their escape. For days, the police refused to investigate properly or to call eyewitnesses to make a statement (later, after I published the story, they did). Since then, I have been denied police protection (unlike most other journalists) and have had to resort to private security.
Soon after the failed ambush, a woman visited my office insisting that I should see her to discuss “the bankers’ designs” on me. I decided to meet with her. She was a frightened woman who claimed to be in grave personal danger. She said that she had been, and was, part of a group comprising former agents and salaried members of the Greek intelligence services, connected to business interests who worked on, at first, wrecking my public image and, later on, planning my physical demise. She added that it was her who, following specific orders, had forged the document ‘proving’ that I was on the payroll of the secret service – a document which her group then circulated to the various blogs that used it.
According to her testimony to me, a group stationed in Skopja was engaged to “see me off”. Part of the same plot concerned the defamation of another woman, a former bank manager with The Bank, who had been fired on false charges of embezzlement because, in truth, she possessed damning evidence concerning The Chairman’s family’s activities. Their plan, vis-a-vis this former bank manager was to plant narcotics in a restaurant that she owned on the island of Zakynthos and to orchestrate a very public arrest so that, in the future, if she ever revealed her evidence against The Chairman’s family, the press could dismiss her as a ‘drug dealer’. To prove her story, my interlocutor handed over a sequence of photographs that were the result of the surveillance of the former bank manager taken by her group. The woman further claimed that she had not dared distance herself from that group but she was afraid that she would be killed upon completing her ‘tasks’.
On our part, we immediately investigated her claims. We subjected her to an accredited graphologist’s test who comfirmed that the forged document showing that I was, supposedly, on the secret agents’ payroll (as published in various blogs) was in her handwriting. We also confirmed with the ferry company that the car in which that team of operatives was supposed to have travelled to Zakynthos (to plant drugs in order to frame The Bank’s former employee) had indeed travelled there. We also established that the car was registered to former intelligence agents who had been prosecuted for an number of misdeeds – and whose court case is pending.
I met with this woman a number of times in an attempt further to establish the truth of her allegations. read more
PHOTOGRAPH: sylvain-emmanuel
Don Giovanni is a certain type of male homosexual. Neither extreme, Tristan or Don Giovanni, is compatible with heterosexual love
March 27, 2013 § 1 Comment

In August 2011, the Japanese company Manuscript was forced to amend the settings of its new software application, Karelog (“Boyfriend Log”), in response to consumer complaints. Drawing on GPS technology, the service allowed users to log in from a computer to track another person’s phone. In the program’s first release, these surveillance capacities also stretched to include accessing the mobile’s call history and remaining battery life. Promotional material for the product targeted anxious girlfriends wanting to know the whereabouts of partners. But within days of the campaign going public, anti-virus software giant McAfee labelled the app a “Potentially Unwanted Program.” This was because users had no way of knowing that the technology had been installed on their device or what information was being logged and sent. The problem was not so much the capacity of the application (GPS tracking is already used for caring purposes of other kinds, such as parents keeping tabs on their children). The crime was that women were encouraged to install the app without partners’ permission. The language of internet security literalised the threat that the program posed as an example of everyday spyware.
Facing the media the president of the fledgling software firm, Yoshinori Miura, admitted the product launch involved some cynicism:
We were still a largely unknown company, so I thought that we could grab attention by focusing on anti-cheating programs, but we went too far. I didn’t think we [would] get so much criticism .
The official apology also addressed the gender assumptions inherent to the application design, since its aesthetics showed clear allegiance to the established traits of Japanese kawaii, or “cute”. Still, press reports admitted that there was nothing about the technology that stopped it from being used by both genders. Steve Levenstein at Inventor Spot wrote:
it takes no knowledge of Japanese to know the pink & lacy graphics at the Karelog website are designed to attract a female demographic. If that’s not enough, check out the image of a big-eyed black kitty (with pink hair bow a la Hello Kitty) gazing longfully at her Android-phone-clutching, pants-wearing tomcat. With that said, there’s no reason why anyone of any gender can use Karelog to spy on anyone of any gender. Let the paranoia-fest begin!
While Boyfriend Log was notable for the headlines it received in English-speaking media, gendered assumptions also affected the release of similar surveillance programs in the US in recent years. iTrust, for instance, is an iPhone application that reveals whether or not a significant other has been tampering with one’s text. In contrast to Boyfriend Log, iTrust turns the tables to allow phone owners to maintain privacy. A fake “home” screen locks the cellphone while its user is absent and records any traces of interfering fingers. In the demo video for the program, a female voice-over describes a failed attempt to read her boyfriend’s text messages in a moment of boredom. Like the men offended by KareLog’s marketing, the casting of a ditzy-sounding girlfriend did not escape the notice of commenters responding to the story on industry stalwart Mashable.
Women are the investigatory agents in each of these examples, whether deliberately, in the case of KareLog, or more casually – indeed, recreationally – in the case of iTrust. The worried partner is gendered female, seen to require stability and transparency through the surveillance of her wandering male. read more
PHOTOGRAPH: [unattributed]
He wasn’t listening. That was the worst of people like that; they were a monologue – killers are like the army, dull and dangerous simultaneously
December 24, 2012 § Leave a comment
Late one Friday evening, my phone played the codec-out sound from Metal Gear Solid, and an email arrived. My stolen laptop had been taken online, and now — like a resourceful kidnap victim — it was phoning home, unknown to its captor. The laptop was beaming back all the information needed to rescue it. And so began one of the strangest episodes so far of my life with technology.
The laptop had been stolen the previous day. I was working in one of the non-public Reading Rooms of the British Library in London. As usual, I left the laptop at my desk when I went to lunch. But this time, when I got back to my desk, it was empty. Damn and blast. CCTV didn’t identify the malefactor, so I went home and changed all my internet-service passwords. I hadn’t lost any work (thanks to Dropbox), but the machine wasn’t insured, and it still felt like a violation — not just of my own distributed, semi-cyborg self, but of the Library as well.
And this wasn’t just any laptop; it was my laptop. It’s not uncommon for us to see personalities in objects, and many people develop a sentimental attachment to their tools. A cook might speak fondly of a particular battered pot, and reminisce about the pungent stews of goats’ feet or bleeding-edge foams made in it; well, this was the Macbook Air on which I’d angrily hammered out my new book, as well as writing tens of thousands of words of other literary and cultural spleen. We’d been through a lot together. Luckily, nine months ago, I had installed some eldritch security software, the open-source Prey. And that’s how, the evening after its abduction, my laptop began calling for help.
I clicked on the link. The Macbook had taken a photograph with its webcam, unknown to the person using it. I saw a young man in an ordinary-looking apartment, shot from a low angle (he was probably using it on his lap) and smiling to someone offscreen. My laptop also told me that he had bypassed my login and created a new user account. A screenshot showed that he was running Apple Software Update. (You don’t want out-of-date system software running on your stolen laptop. That would just be embarrassing.) Triangulating local wifi signals, the laptop reported a rough location on a Google map: a street in Stratford, east London. It told me its router’s IP address, and the name of the wifi network it was connected to. “Friendz.” That just added insult to injury. These clowns nick my laptop, and call their home network “Friendz”? With a Z? Seriously? I might have had some respect for them as criminals if they had called it “Raffles”. Or even “Hamburglar”.
To receive this report was both amazing and deeply odd. Thanks to Prey’s stealth technology, I was now engaged in an amateur police surveillance action, a voyeuristic keyhole-peeping. I forwarded the information to the law-enforcement professionals, the Metropolitan Police, but I couldn’t shake another weird feeling. I knew it was just a machine running instructions, but it felt as though my computer was sentient, and pleading in a faint but very precise voice to be liberated. It was, I decided, uncanny. More than that, it was a uniquely modern species of the uncanny that in Freud’s day simply wasn’t possible: spying in near-real-time on a thief, by means of the stolen object itself, which had, or so it seemed, come to life. Call it the cyber-uncanny. read more
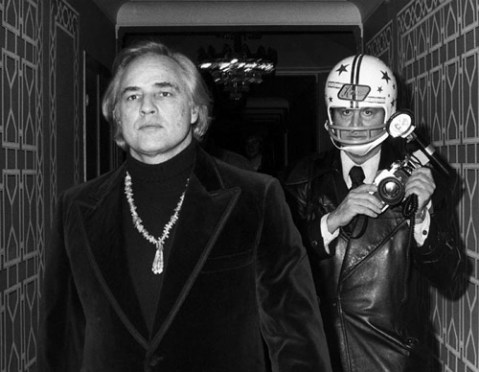
PHOTOGRAPH: Ron Galella

